The Growing Importance of Device Security

Security threats to devices like laptops, mobile devices, and POS systems are becoming more frequent and sophisticated. Understanding these threats—such as malware, phishing, and data breaches—can help you better protect your devices and data. In this post, we’ll cover the top security threats to devices and how you can safeguard against them.
Don’t wait for an attack—protect your devices today!
1. Malware: The Invisible Predator
What Is Malware?
Malware is a malicious program designed to infiltrate devices, steal data, or disrupt operations. It comes in various forms, including:
Signs Your Device Might Be Infected
- Slower performance or frequent crashes.
- Unauthorized data access or strange pop-ups.
- Increased internet data usage without explanation.

How to Protect Against Malware
- Install Reputable Security Software: Norton, Kaspersky, or Bitdefender.
- Update Regularly: Software patches fix known vulnerabilities.
- Be Wary of Downloads: Avoid clicking on unsolicited links or opening suspicious attachments.
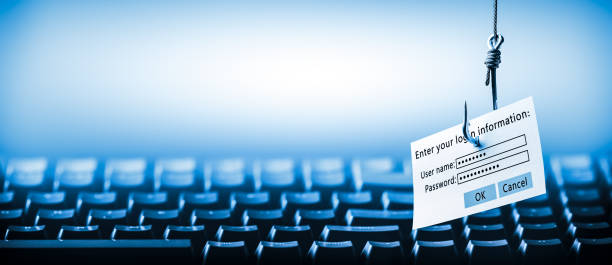
2. Phishing: The Master of Deception
How Does Phishing Work?
Phishing uses fake communications to trick users into revealing sensitive information such as passwords or credit card details. These attacks can come through:
- Emails: “Your account has been compromised. Click here to reset your password.”
- Text Messages: Fake delivery notifications or banking alerts.
- Social Media: Fraudulent ads or fake profiles.
Prevention Tips
- Verify the sender’s email address before clicking any link.
- Use anti-phishing browser extensions like Avast Online Security.
- Train employees with simulated phishing campaigns.
3. Data Breaches: The Ultimate Price of Neglect
What Are Data Breaches?
Data breaches occur when unauthorized individuals access confidential information, often targeting poorly secured systems. This can lead to financial loss, reputational damage, and legal consequences.
How to Minimize Risk

- Encrypt all sensitive data, whether stored locally or in the cloud.
- Implement Zero Trust Security Models—never trust, always verify.
- Implement Strong Authentication Practices
4. Unsecured Networks: An Open Invitation for Hackers
The Danger of Public Wi-Fi
Unsecured networks, like those in cafes or airports, are breeding grounds for cybercriminals. Hackers can intercept data transmitted over these networks, leading to:
- Credential theft (e.g., email or banking logins).
- Unauthorized device access.
- Distribution of malware.
How to Stay Safe on Public Networks
- Use a VPN (Virtual Private Network) to encrypt your data.
- Turn off automatic Wi-Fi connections.
- Avoid accessing sensitive accounts on public networks.
5. Physical Theft: The Simplest Cyber Threat
Why Physical Security Matters
A stolen laptop, phone, or POS device can result in both hardware loss and exposure of sensitive data.
Proven Protective Measures
- Use cable locks for laptops in public spaces.
- Enable remote wipe capabilities for all devices.
- Activate device tracking features like “Find My Device.”

Pro Tip:
For POS systems, implement biometric authentication to prevent unauthorized access.
Expert Solutions from Eksani Systems
At Eksani Systems, we specialize in cybersecurity solutions tailored to protect laptops, mobile devices, and POS systems. From real-time threat monitoring to advanced encryption services, we have your back.
What We Offer:
- Advanced POS system protection.
- Endpoint security for laptops and mobile devices.
- Comprehensive cybersecurity audits.
Cyber threats are evolving rapidly. Whether it’s malware, phishing, or physical theft, staying informed and implementing preventive measures is essential. By partnering with a trusted cybersecurity expert like Eksani Systems, you can protect your devices and data from the dangers of today’s digital landscape.